Background on the NIST Cybersecurity Framework
The NIST Cybersecurity Framework (CSF) is a voluntary, risk-based framework that provides a structured approach for organizations to identify, manage, and reduce cybersecurity risks. Developed collaboratively by industry experts, academic institutions, and U.S. government stakeholders, the NIST CSF has become one of the most widely adopted and adaptable frameworks for improving security posture, particularly in critical infrastructure and industrial environments.
Originally published in 2014, the framework was designed to provide a common language and reference model for cybersecurity activities. Its flexible structure allows organizations of all sizes and maturity levels to adopt it, regardless of their sector or existing security model.
In February 2024, NIST released Version 2.0, marking the first major update in a decade. This new version builds on the strengths of its predecessor while incorporating feedback from global practitioners and lessons learned from years of real-world application. The updated framework reflects the evolving nature of cybersecurity threats and the growing importance of governance, supply chain risk, and enterprise-wide integration.
Its continued relevance is reflected in industry adoption trends: according to the SANS 2021 OT/ICS Cybersecurity Survey, nearly 48% of respondents reported using the NIST CSF to guide their OT/ICS cybersecurity practices, making it the most widely used framework in that domain.
Why It Matters for OT/ICS Organizations
For organizations operating Operational Technology (OT) and Industrial Control Systems (ICS), the NIST CSF offers:
- A structured way to align cybersecurity efforts with operational goals
- A common reference point for IT, OT, and executive leadership
- Flexibility to tailor controls based on operational constraints and maturity
At Enaxy we’ve helped clients across energy, manufacturing, and infrastructure sectors operationalize the NIST CSF in OT environments balancing compliance, safety, and performance. Our team can help assess readiness, map the CSF to your existing controls, and build an implementation roadmap that works in the real world.
Overview of the NIST Cybersecurity Framework
The NIST CSF consists of three main components:
1. CSF Core
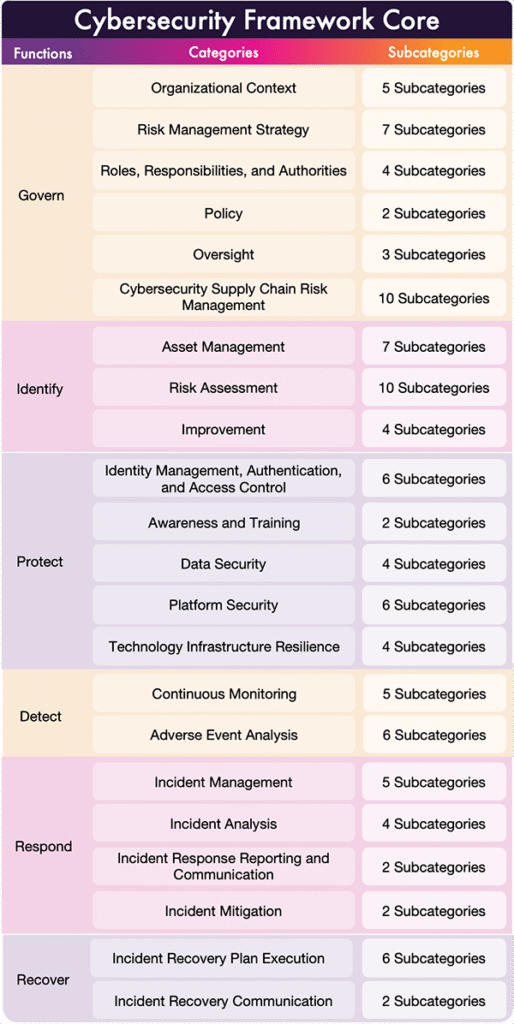
The CSF Core is a taxonomy of high-level cybersecurity outcomes organized into six Functions: Govern, Identify, Protect, Detect, Respond, and Recover. Each function is further divided into categories and subcategories that detail their specific cybersecurity outcomes.
2. CSF Organizational Profiles
A CSF Organizational Profile captures an organization’s current and/or target cybersecurity posture, structured around the outcomes defined in the CSF Core. Profiles help bridge the gap between high-level objectives and operational activities by allowing organizations to:
– Assess where they are today (Current Profile)
– Define where they need to be (Target Profile)
– Prioritize efforts to close the gap
– Communicate clearly across teams and stakeholders
3. CSF Tiers
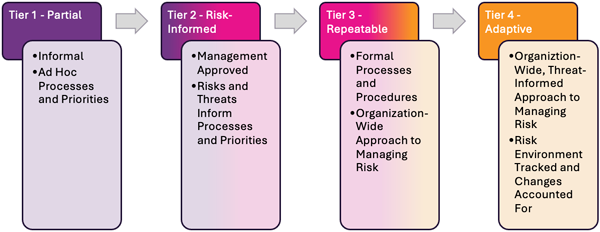
The Tiers describe the level of formality, integration, and sophistication in an organization’s approach to cybersecurity risk management. Version 2.0 retains the four-tier model:
– Tier 1: Partial
– Tier 2: Risk-Informed
– Tier 3: Repeatable
– Tier 4: Adaptive
Each tier reflects how rigorously an organization integrates cybersecurity into decision-making, governance, and operations. Tiers are commonly applied to Organizational Profiles to help define both current and target states.
It’s important to note that Tiers are not maturity levels to be “maxed out.” While CSF 1.1 explicitly stated that Tiers were not a maturity model, that language was removed in version 2.0 but the intent remains: the goal is not to reach Tier 4 across the board, but to choose the Tier that aligns with your risk environment and operational context.
Benefits of Using the NIST Cybersecurity Framework
The NIST CSF offers several key benefits, especially among organizations managing industrial control systems and critical infrastructure operations. Here are five core benefits of adopting the NIST CSF:
- Flexible, Sector-Agnostic Design
The CSF is built around high-level cybersecurity outcomes that can be tailored to any sector or organization. Whether you’re operating a water treatment plant, electric utility, or manufacturing facility, the CSF enables you to adapt its guidance to your unique risks, regulatory landscape, and operational environment without forcing a rigid checklist. - Structured Risk Management
The framework provides a systematic approach to identifying, assessing, and prioritizing cybersecurity risks, while also mapping them to business objectives and tolerances. This helps organizations manage security like any other business risk, making it easier to align executive decision-making and operational planning. - Enhanced Communication and Collaboration
The CSF’s use of standardized terminology and outcome-based language improves communication across departments, especially between IT, OT, leadership, and external stakeholders. It also enables more consistent engagement with regulators, partners, and service providers. - Baseline for Benchmarking and Improvement
Organizations can use the CSF’s Profiles and Tiers to define their current and target cybersecurity states. These tools support self-assessment, maturity modeling, and progress tracking, making it easier to identify gaps, prioritize improvements, and demonstrate growth over time. - Regulatory Alignment and Compliance Enablement
Many government agencies and industry bodies have incorporated the NIST CSF into their cybersecurity requirements, making it a valuable tool for maintaining compliance. Even in those cases where complying with the CSF is not explicitly required, the statutory requirements are often mapped to the Framework.
Challenges in Implementing the NIST Cybersecurity Framework
While the NIST CSF is a flexible and widely respected tool for improving cybersecurity posture, adopting and operationalizing it within real-world OT/ICS environments can be challenging—especially for organizations with limited resources or lacking specialized expertise. Here are the most common hurdles organizations encounter:
- Translating the Framework into Action
The NIST CSF provides high-level outcomes, not prescriptive checklists. This makes it easily adaptable but also difficult to interpret and implement without guidance. For many organizations, particularly those newer to cybersecurity or working with legacy OT systems, translating abstract categories and subcategories into concrete, actionable steps can be overwhelming. Mapping CSF outcomes to specific technologies, control procedures, and operational risks requires not only cybersecurity fluency but also deep knowledge of the OT domain. - Resource and Capability Constraints
Even with the best intentions, implementing the CSF requires time, funding, and skilled personnel, resources that are often limited in smaller or mid-sized organizations. Building a sustainable cybersecurity program involves more than checking boxes; it requires cross-functional engagement, regular training, policy development, and continuous improvement cycles. This resource gap can slow progress or lead to fragmented implementations that miss the full value of the framework. - Absence of Descriptive Names for Subcategories
One notable design decision in NIST CSF 2.0 is the continued use of reference numbers and text descriptions for Subcategories, without assigning them concise, descriptive names. This approach introduces practical challenges during implementation because the lack of named sub-categories requires that either your audience already knows what the subcategory identifiers refer to (e.g., what is ID.AM-03 referring to?) or that full text descriptions of subcategories need to be repeatedly referenced which can become cumbersome in documentation, team discussions, or training materials. - Measuring and Demonstrating the Value
One common implementation challenge is quantifying the impact of the NIST CSF. Unlike a single security tool or technology, the CSF is a strategic framework and its benefits often emerge over time through improved governance, reduced risk exposure, and stronger incident response. - US-Centric Background
Although the NIST CSF has gained international recognition, its origin in the United States and alignment with U.S. policy frameworks can cause hesitation for multinational organizations, particularly among non-U.S. business units or regulatory bodies.
Next Steps for Implementing the NIST Cybersecurity Framework
Whether you’re just beginning your cybersecurity journey or looking to refine and operationalize your program, Enaxy is here to help you maximize the value of the NIST Cybersecurity Framework (CSF). Our team brings deep expertise in critical infrastructure and OT/ICS environments, ensuring that your implementation is both effective and practical.
We offer tailored support across all phases of CSF adoption, including:
- Cybersecurity Assessment and Gap Analysis
Understand where you stand today. We’ll assess your current cybersecurity posture against the CSF to uncover strengths, identify gaps, and highlight opportunities for meaningful improvement. - Customized CSF Organizational Profiles
We help you define your Current Profile and Target Profile, translating CSF outcomes into a roadmap that aligns with your strategic goals, regulatory obligations, and risk appetite. - Integration with Existing Risk and Compliance Programs
Already working with ISO 27001, NERC CIP, or sector-specific standards? We’ll map and integrate the CSF with your existing governance, risk, and compliance structures ensuring efficiency and cohesion. - Training and Enablement
We provide customized training sessions for technical teams, business leaders, and cross-functional stakeholders to build buy-in, promote consistency, and enable confident adoption. - Progress Monitoring and Reporting
We’ll establish meaningful KPIs and provide ongoing support to track your CSF implementation progress, demonstrate ROI, and adapt over time as your environment evolves.
To schedule a consultation or learn more, email us at info@enaxy.com. We’d love to support your journey toward a more resilient, risk-informed cybersecurity program.