Operational Technology (OT) and Industrial Control Systems (ICS) are critical to the infrastructure powering our modern lives, from electricity grids and water systems to manufacturing plants and transportation networks. As cyber threats targeting these systems evolve, security professionals should always be considering how their approach to securing OT/ICS systems should adapt. The terminology that we use to describe what we do may also need to evolve to better describe these new approaches, as the words we use are not only descriptive but can also help to drive what we do in our day-to-day jobs. A longstanding term Network Security Monitoring (NSM) has traditionally captured what leading cybersecurity solutions for OT/ICS environments deliver. But is “NSM” still the best description of today’s market reality?
Let’s unpack this question by exploring recent shifts in the OT/ICS cybersecurity landscape and examining current offerings from industry leaders like Dragos, Claroty, Tenable, Forescout, Nozomi Networks, and emerging vendors like Frenos.
ICS NSM: What’s In a Name?
Historically, Network Security Monitoring, as popularized by the Father of NSM Richard Bejtlich, focused on continuous monitoring of network traffic, rather than relying solely on endpoint detection or traditional antivirus. It was adapted by OT/ICS cybersecurity vendors because for a long-time security companies were discouraged from actively connecting to ICS networks out of fear of unintentionally impacting the operations of the network. The earliest companies in this market were founded in the late 2000s to early 2010s. This market segment rapidly became the leading product category in OT/ICS cybersecurity. By 2017 consultant and S4 founder Dale Peterson wrote an article titled Insanely Crowded ICS Anomaly Detection Market where he identified 22 different companies, with most of them focused on passive network monitoring. Throughout the late 2010s, the leading vendors often used the more general term of NSM than Anomaly Detection because they could incorporate other aspects, such as passively gathering asset inventory information, that “Anomaly Detection” by itself misses. While effective, the term NSM implies a largely passive, reactive stance that might no longer accurately describe the comprehensive, proactive capabilities modern solutions offer.
Modern platforms now integrate proactive threat hunting, risk assessment, vulnerability management, secure remote access, and deep integration with broader enterprise security frameworks. So perhaps it’s time for a change. Should we move beyond NSM to a broader, more inclusive terminology?
Beyond Asset Inventory
Traditionally, asset inventory and visibility have been the core use cases driving adoption of ICS NSM platforms. Organizations have prioritized understanding what’s on their networks, given that you can’t secure what you can’t see. Anecdotally, maintaining an up-to-date asset inventory based on passively monitoring the network was the leading feature that impacted decisions to buy the products.
However, asset inventory alone is now a baseline expectation rather than a differentiator. Enterprises now demand capabilities that offer proactive defense, predictive threat analytics, and deeper integrations into enterprise security operations.
Leading use cases for modern OT cybersecurity platforms now include:
1. Vulnerability Management & Risk Reduction
Simply building an asset inventory is not the main goal, but rather the goal is to use the information learned about the entire controls environment and identify prioritized, actionable steps that can be taken to reduce the risk of security or operational issues and increase the resiliency of the OT/ICS environment.
2. Threat Detection and Response (TDR)
Vendors are emphasizing advanced threat detection and comprehensive incident response capabilities, leveraging industrial-specific threat intelligence to detect, respond, and mitigate incidents swiftly and effectively.
3. Reduced Attack Surface & Segmentation
Reducing the attack surface by controlling access at the network edge and reducing the ability for cyber attacks to spread based segmentation is becoming increasingly essential in ICS cybersecurity.
4. Secure Remote Access & Operations
Recent shifts toward remote work (and the associated cost savings) have heightened demand for secure remote operational capabilities. Vendors are addressing this need by providing solutions tailored specifically for secure remote access and real-time monitoring of industrial control environments, often as a new product offering from the “traditional” OT/ICS security vendor.
5. Enterprise-Wide Visibility
OT systems are becoming more interconnected with other enterprise networks, and executives are trying to identify risks and threats using a whole-of-enterprise viewpoint. This is leading to traditional IT cybersecurity vendors adding ICS cybersecurity expertise, and OT cybersecurity vendors finding ways to partner with and share data to enterprise-wide security and risk dashboards.
What’s A Better Name Than NSM?
Given this evolution, what should we call the ICS NSM market today? Here are some possible names reflecting current capabilities and market direction:
- Industrial Cybersecurity Platform (ICP) – Emphasizes comprehensive protection beyond passive monitoring.
- Operational Technology Security Management (OTSM) – Highlights proactive management of security across OT assets.
- Cyber-Physical Systems Threat Management (CPSTM) – Focuses clearly on threat detection, prevention, and response.
- Industrial Cyber Risk Management (ICRM) – Prioritizes proactive risk management and vulnerability reduction, aligning with enterprise risk frameworks.
Each of these terms captures the shift toward proactive, integrated capabilities extending beyond mere network monitoring. You could mix-and-match the nouns and verbs between each term, too. For example, maybe you prefer OT Cyber Risk Management (OTCRM).
Where Are Vendors Heading?
Leading vendors already reflect this shift1
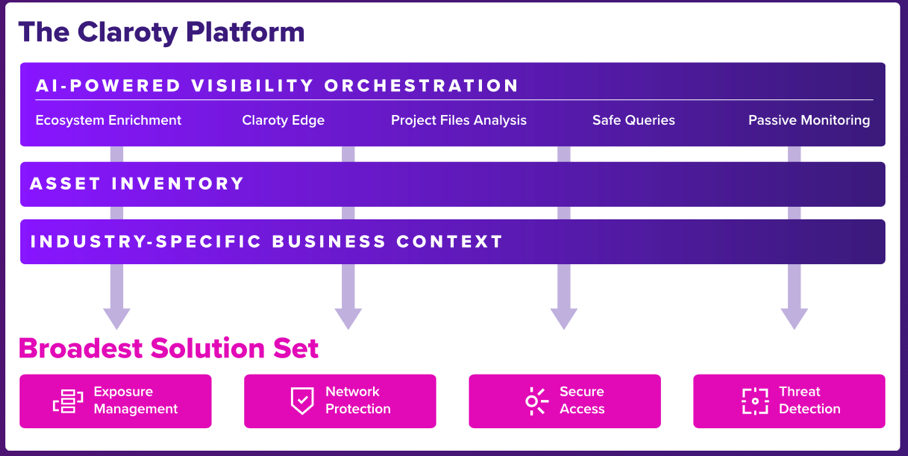
- Claroty highlights the breadth of different products offered by their Platform, ranging from secure remote access to exposure management and threat detection.
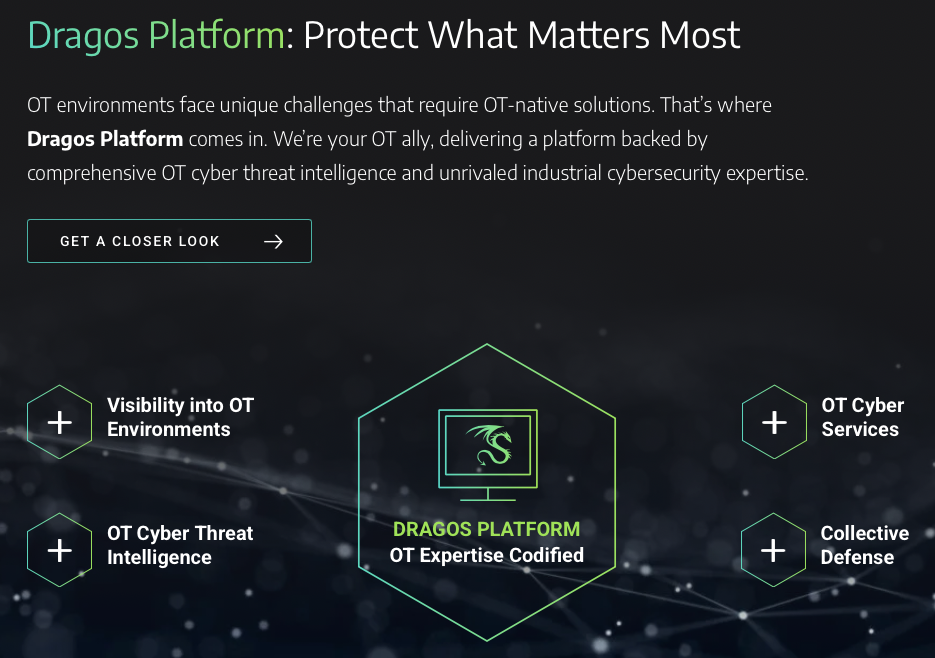
- Dragos has positioned itself as a Platform providing both OT cybersecurity products and services. They emphasize threat intelligence, proactive threat hunting, and integrated incident response.
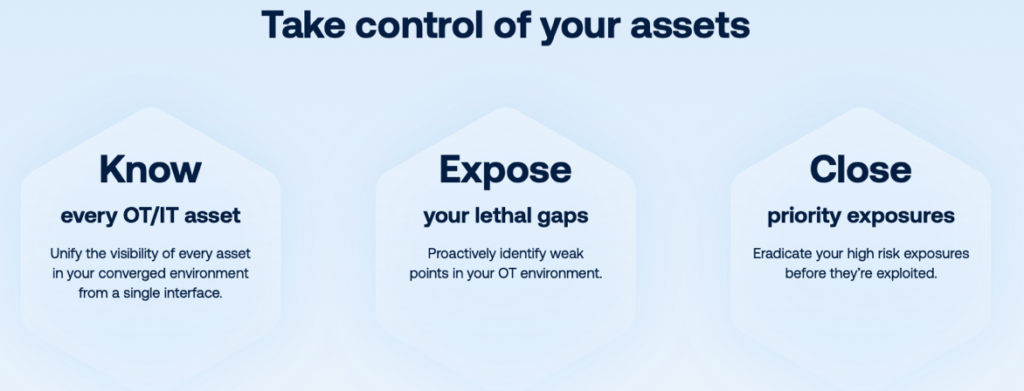
- Forescout was originally an IT cybersecurity company that acquired one of the leading ICS NSM companies in 2018 (SecurityMatters), so they’re no longer just a pure-play ICS/OT cybersecurity company. With the combined focus on both IT and OT, their marketing focuses on managing risk across the enterprise.

- Frenos is an emerging player and unique among these companies by using the information provided by other cybersecurity tools2 instead of actively monitoring the network themselves. Like the others, they refer to their Platform in marketing and focus on prioritizing risk reduction activities based on real-world threat scenarios and tailored advice based on potential attack paths.

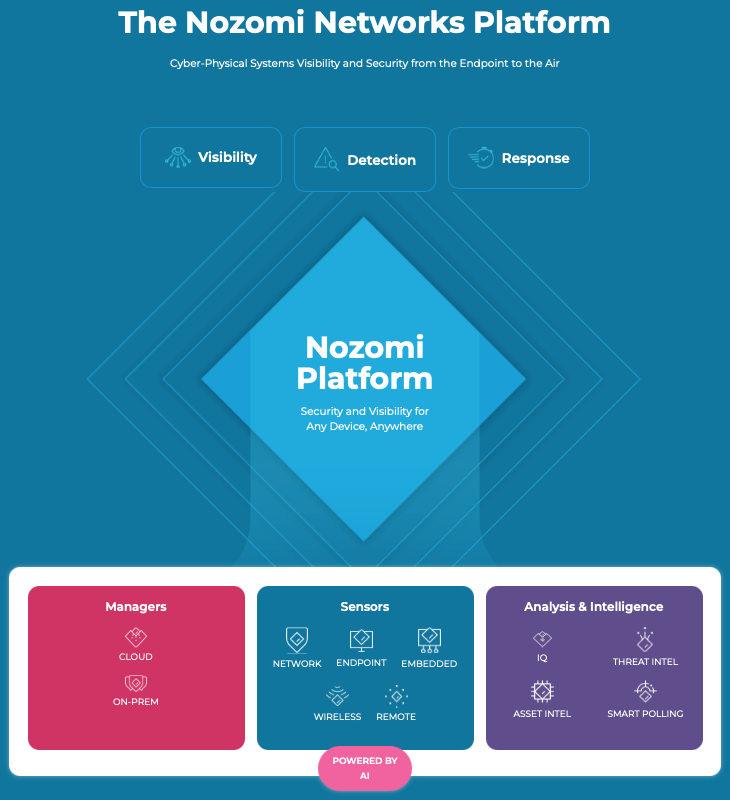
- Nozomi Networks also refers to their Platform on their Product page instead of focusing on individual product offerings. I think there is a theme here.
- Tenable leverages deep integration between asset management and proactive vulnerability assessments. Like Forescout, they are also a traditional IT cybersecurity company, and so their marketing leans into the enterprise-wide integration of cybersecurity programs.
Clearly, the market is embracing a broader, more integrated approach to securing industrial environments, indicating a more comprehensive term might soon replace “ICS NSM.”
Conclusion: Evolving Beyond NSM
While the term ICS NSM is familiar, today’s cybersecurity realities demand a new vocabulary one reflective of proactive defense, integrated threat management, and comprehensive cyber resilience. Terms like Industrial Cybersecurity Platform or Industrial Threat Management better capture the proactive, integrated approach companies require in today’s increasingly sophisticated threat landscape.
Perhaps it’s time for the industry to move beyond NSM, embracing terminology that fully captures the reality and ambition of contemporary industrial cybersecurity.
Ultimately, this shift in terminology signifies more than just market semantics; it highlights a fundamental evolution in the expectations and needs of modern OT/ICS cybersecurity. Leading practitioners are no longer merely observing their OT/ICS networks, they’re actively defending, responding, and empowering organizations to proactively manage and secure their most critical operational assets.
At Enaxy, we help critical infrastructure organizations transition from reactive monitoring to proactive, integrated cyber defense. Whether you’re looking to reframe your program strategy, assess your current capabilities, or implement an industrial cybersecurity platform tailored to your operations. We’re here to help. Contact us at info@enaxy.com to start a conversation about how to modernize and strengthen your industrial cybersecurity posture.
1Alphabetical listing so as to not play favorites.
2In fact, each of the other companies listed here are included in the Frenos website’s Partners page.