In today’s complex and highly interconnected Operational Technology (OT) and Industrial Control System (ICS) environments, network visibility is not a luxury it’s a necessity. Industrial networks are the backbone of operations across energy, utilities, manufacturing, transportation, and critical infrastructure sectors. They support the reliable, safe, and continuous flow of data between sensors, controllers, workstations, and management systems.
Yet, despite their importance, many industrial environments lack the ability to observe, inspect, and analyze real-time network traffic, leaving them blind to performance bottlenecks, misconfigurations, cyber threats, and policy violations. This lack of visibility can compromise uptime, threaten physical safety, and jeopardize regulatory compliance.
To address this gap, organizations turn to traffic mirroring technologies that allow them to monitor communications in real time without interrupting production. In this series, we’ll explore two of the most widely adopted methods:
- SPAN (Switched Port Analyzer), a software-based mirroring feature available on managed switches, and
- Network TAPs (Test Access Points), purpose-built hardware devices designed for high-fidelity traffic capture.
Applications of Network Visibility in Industrial Environments
Visibility isn’t just a cybersecurity function, it’s essential for operational success. When deployed strategically, monitoring tools can deliver major gains across key industrial objectives:
- Real-Time Monitoring & Troubleshooting
Gain continuous insight into traffic flow between devices across distributed environments, enabling rapid isolation of faults and faster recovery from unexpected issues. - Performance Optimization
Analyze throughput, latency, packet loss, and jitter to identify congestion, fine-tune configurations, and optimize critical network paths. - Threat Detection & Prevention
Integrate mirrored traffic with Network Security Monitoring (NSM), Intrusion Detection Systems (IDS), and Security Information and Event Management (SIEM) tools to detect and contain threats before they escalate. - Regulatory Compliance
Generate audit trails and evidence for standards like NERC-CIP, IEC 62443, TSA pipeline directives, and others. Continuous monitoring supports policy enforcement and incident forensics.
What Is SPAN?
SPAN (Switch Port Analyzer) (often referred to as port mirroring) is a feature embedded in many managed switches. Originally introduced by Cisco, SPAN allows traffic from one or more ports or VLANs to be duplicated and sent to a designated monitoring port.
This mirrored traffic can be captured by tools such as packet analyzers, NSM platforms, or protocol decoders, allowing organizations to monitor communications without disrupting live operations.
Important Note: A common misconception is that SPAN ports are receive-only. In reality, many switch vendors allow bidirectional traffic on mirror ports by default. One vendor has the option to turn on and off bidirectional traffic on mirror ports. Always verify your switch’s behavior and configuration to avoid unintentional risk exposure.
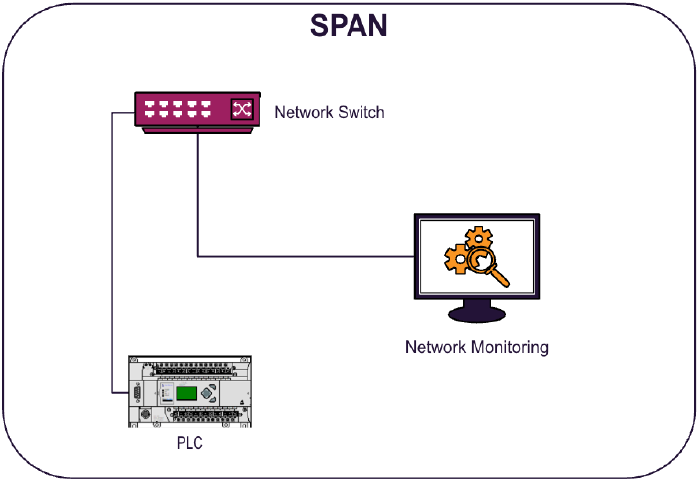
SPAN Variants
- Local SPAN: Mirrors traffic within a single switch.
- RSPAN (Remote SPAN): Extends mirroring across multiple switches via a special VLAN.
- ERSPAN (Encapsulated RSPAN): Sends mirrored traffic over routed IP networks using GRE tunnels, ideal for centralized or remote monitoring.
Key Benefits of SPAN
- Cost-Effective: Uses existing switch hardware, no added equipment required.
- Quick to Deploy: Software configuration on most managed switches.
- Flexible: Can mirror ports, VLANs, or traffic types.
- Non-Disruptive: Operates without impacting live network operations.
- Scalable: Easily adjusted as network needs evolve.
Limitations of SPAN in OT/ICS Networks
Despite its advantages, SPAN has notable constraints in high-demand environments:
- Packet Loss: Switches may drop mirrored packets under heavy traffic loads to preserve live traffic performance.
- Resource Overhead: SPAN consumes switch CPU cycles, which can affect switch performance if overused.
- Limited Port Support: Some switches only allow a small number of concurrent mirror sessions.
- Device Dependency: SPAN relies on the presence and capability of managed switches.
- Stability Risks: RSPAN/ERSPAN can introduce instability if misconfigured or overused.
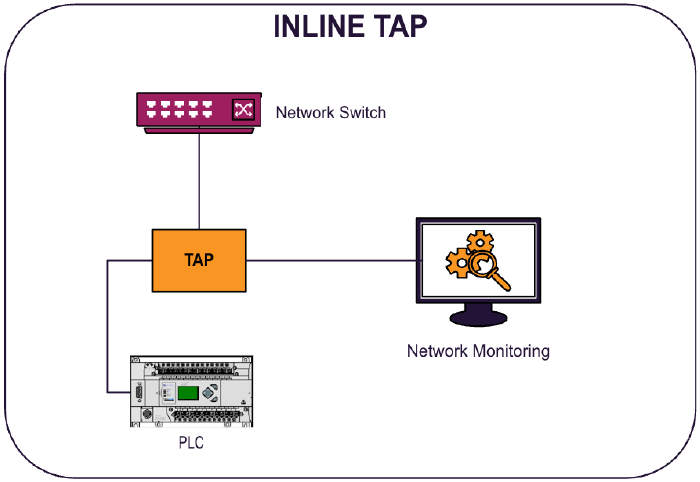
What Are Network TAPs?
A Network TAP (Test Access Point) is a dedicated, inline hardware device that passively captures all network traffic between two connected devices without affecting that traffic in any way. TAPs are completely independent of switch configurations and are designed for lossless, high-fidelity monitoring.
TAPs work by duplicating each data packet traversing the network link and sending a copy to a monitoring port for analysis. This ensures complete visibility and is especially critical in mission-critical or compliance-sensitive OT/ICS environments.
Types of TAPs
Inline TAPs
- Placed directly between two network devices (e.g., PLC and switch)
- Capture all inbound and outbound packets
- Fail-open capable to preserve network continuity during power loss
- Suitable for copper and fiber links
Passive TAPs
- Often used in fiber networks
- Do not require traffic interruption to install
- Capture traffic without introducing latency or interference
- Cannot inject traffic, monitoring only
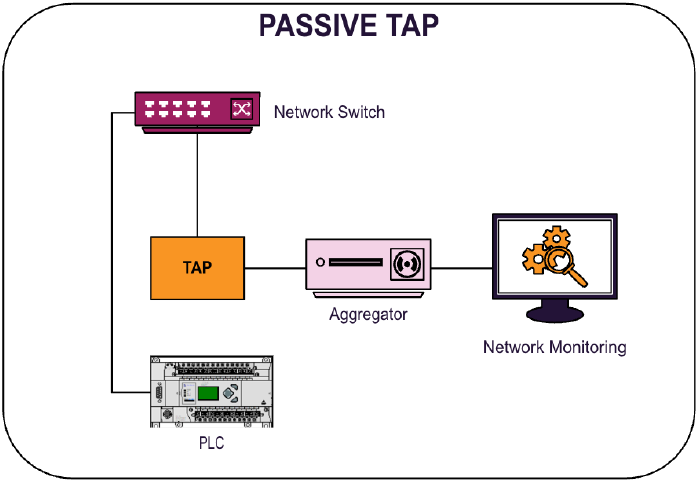
Why TAPs Matter in Industrial Networks
Key Benefits of TAPs
- Security: Delivers full-packet, real-time data to security tools, improving threat visibility and forensic capability.
- Reliability: Provides zero-packet-loss capture, even under high-load conditions which is ideal for deterministic systems and safety-critical processes.
- Compliance: Supports high-integrity logging required for audits and regulatory validation.
- Diagnostics: Offers granular, packet-level visibility for deep troubleshooting and network behavior analysis.
- Independence: Operates without relying on switch capabilities or consuming network resources.
Selecting the Right TAP
Choosing the right TAP for your environment depends on several technical and operational factors:
- Network Speeds: Support for 100 Mbps, 1G, 10G, 40G, or higher
- Media Type: Copper vs. fiber (single-mode or multi-mode)
- Port Density: Number of links to monitor concurrently
- Fail-Safe Features: Fail-open operation in the event of power loss
- Compatibility: Integration with your existing monitoring or security stack
SPAN vs. TAP – Which is Right for You?
Both SPAN and TAP technologies play critical roles in modern industrial network monitoring. Each has its place depending on the use case, infrastructure maturity, performance requirements, and risk tolerance.
- Use SPAN for rapid deployment, cost-sensitive environments, or when broad visibility is needed without additional hardware.
- Use TAPs when data accuracy, lossless capture, or regulatory compliance is essential, especially in high-security or mission-critical applications.
How Enaxy Can Help
At Enaxy, one of the services we specialize in is helping industrial organizations design, implement, and optimize network visibility strategies tailored to their unique OT and ICS environments. From assessing existing infrastructure to deploying the right mix of SPAN or TAP solutions, our team brings deep, hands-on experience to ensure alignment with your operational, security, and compliance goals.
Have questions about deploying SPAN or TAP in your environment?
We’re here to help, reach out to our team at info@enaxy.com to start the conversation.Stay tuned for the next installment in this series, where we’ll provide a side-by-side comparison of SPAN and TAP technologies, followed by real-world case studies showcasing how Enaxy has helped clients overcome deployment challenges and achieve full network visibility in complex OT/ICS networks.