Cellular connectivity has quietly become one of the most common yet least understood components in modern OT environments.
Utilities, oil and gas operators, manufacturers, and transportation providers are deploying hundreds or thousands of cellular modems to connect remote assets, including pumps, RTUs, PLCs, meters, sensors, and mobile equipment. The appeal is clear: fast deployment, wide coverage, and minimal reliance on existing infrastructure.
But while cellular addresses availability and reach, it also introduces a unique and often underestimated cybersecurity risk profile that doesn’t align cleanly with traditional IT or OT security assumptions.
Managing risk at scale requires moving beyond “it’s private cellular” or “the carrier handles security” and treating cellular modems for what they are: distributed, internet-connected OT edge systems.
Why Cellular Is Different in OT
From a risk perspective, cellular modems don’t behave like typical OT network components.
They are:
- Deployed outside controlled facilities
- Often physically accessible to the public
- Routinely managed by third parties
- Updated infrequently, if at all
- Connected through complex carrier and Access Point Name (APN) architectures
Unlike traditional OT network equipment installed inside substations, control rooms, or locked cabinets, cellular modems are often deployed in locations accessible to the public.
They may be mounted on:
- Roadside cabinets
- Pole-mounted enclosures
- Remote pump stations
- Mobile or temporary installations
In many cases, physical access does not require bypassing fences or alarms, only time and curiosity.
Physical access changes the threat model. An attacker does not need to defeat network controls if they can:
- Power-cycle the device
- Remove or swap the SIM
- Reset the modem to factory defaults
- Access exposed debug or management ports
Once physical control is obtained, logical protections such as private APNs and firewall rules may no longer matter.
This is why cellular modems in OT environments must be treated as potentially hostile edge devices rather than trusted infrastructure components.
In many cases, the modem becomes:
- The only network boundary protecting the asset
- The only managed device between the field and control systems
- The least monitored component in the environment
This combination creates a gap between perceived security and actual exposure.
Common Risk Blind Spots in Large Deployments
“Private APN” Is Not a Security Control
Private APNs are often treated as a security silver bullet.
They do provide traffic segregation from the public internet, but they do not:
- Prevent modem compromise
- Stop malicious firmware
- Protect weak management interfaces
- Detect misuse of credentials or SIMs
If an attacker compromises the modem, the APN becomes irrelevant. The trust boundary has already been breached.
Risk takeaway: APNs reduce exposure, not risk.
Modems Become Shadow Infrastructure
In large deployments, modems are often:
- Procured by engineering
- Installed by contractors
- Managed by telecom teams
- Forgotten by cybersecurity
Over time, organizations lose visibility into:
- What models are deployed
- Which firmware versions are running
- Which credentials are configured
- Which devices are still active
Dormant SIMs, abandoned devices, and undocumented replacements are common, and they persist for years.
Risk takeaway: Unknown cellular assets are high-risk assets.
Management Interfaces Are the Weakest Link
Most cellular modems expose:
- Web interfaces
- SSH or Telnet access
- Remote management agents
- SMS-based control features
In OT environments, these interfaces are frequently:
- Left with default credentials
- Exposed over the carrier network
- Shared across hundreds of devices
- Unmonitored
A single leaked password can compromise an entire fleet.
Risk takeaway: At scale, credential reuse is a systemic vulnerability.
Firmware Risk Is Rarely Operationalized
Firmware updates in OT cellular deployments are difficult:
- Devices may be remote or powered intermittently
- Updates risk interrupting operations
- Change windows are limited or nonexistent
As a result, organizations accept:
- Years-old firmware
- Known vulnerabilities
- Unsupported modem models
The risk isn’t just exploitation, it’s fragility. When something breaks, recovery options are limited.
Risk takeaway: Unsupported firmware poses both security and reliability risks.
Designing Cellular Modem Access for Third-Party Data Use
At scale, cellular modems are rarely used only by the asset owner.
Vendors, OEMs, system integrators, analytics providers, and support teams often need remote access to data for:
- Performance monitoring
- Predictive maintenance
- Regulatory reporting
- Vendor support contracts
The mistake organizations make is treating third-party access as an exception rather than a design requirement.
When access is bolted on later, risk grows exponentially.
Reference Architecture: Secure Cellular Access Without Extending Trust to the Edge
The most effective way to manage third-party access at scale is to design it into the architecture from the beginning.The reference architecture below illustrates a defensible, repeatable pattern for cellular-connected OT assets that enables data sharing without turning field modems into trusted gateways.
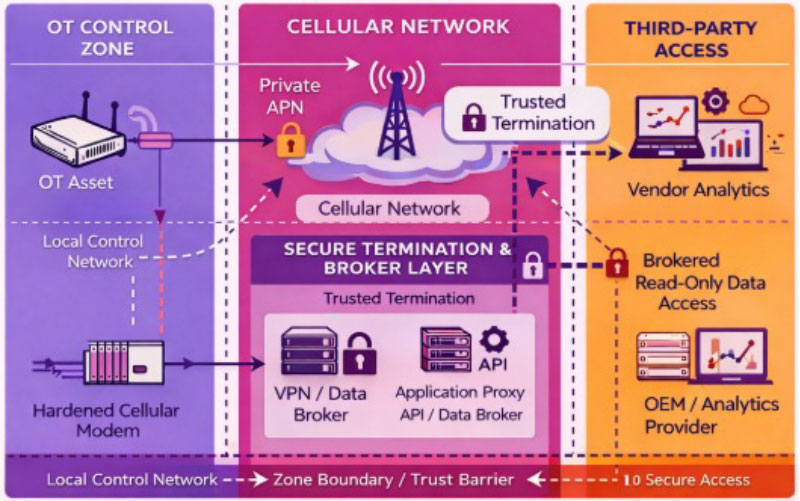
Image 1 – Secure Cellular Modem Architecture for OT Network
Cellular-connected field assets publish data through hardened modems over private carrier infrastructure to a controlled termination layer (DMZ or broker). Third parties consume brokered data without direct access to modems or OT networks.
What This Architecture Enforces
- Cellular modems are used strictly for transport, not trust
- No third-party access terminates at the modem or field asset
- Vendor and partner access ends in a broker or DMZ layer
- OT control zones remain isolated regardless of external access needs
This architecture ensures that a compromised modem does not compromise the control system and that third-party access can be revoked centrally without touching field equipment.
Design Rule:
If a third party can directly access a cellular modem, trust has already been extended too far.
Step 1: Decide What the Third Party Actually Needs
The following steps assume an architecture like Image 1 – Secure Cellular Modem Architecture for OT Network, where third-party access is intentional, brokered, and isolated from OT control zones.
Start with a simple but often skipped question:
Do they need data, or access?
In many cases, third parties:
- Do not need interactive access to the modem
- Do not need network-level connectivity
- Only need periodic telemetry or status data
Whenever possible:
- Push data outward via controlled channels
- Avoid inbound access entirely
- Treat the modem as a one-way publisher, not a gateway
Design rule:
If a third party can do their job without logging into your modem, don’t give them a login.
Step 2: Separate Transport from Trust
A common anti-pattern is allowing third parties onto the same APN or routing domain used for internal OT communications.
Instead:
- Use logical separation between internal OT traffic and third-party data flows
- Terminate third-party access in a DMZ or brokered service
- Avoid routing vendor traffic directly into control system zones
This can be achieved using:
- VPN termination points upstream of the OT network
- Data brokers or message queues
- API-based data sharing instead of raw network access
Key principle:
Third parties should consume data outputs, not participate in your network.
Step 3: Never Share Modem Credentials
At scale, shared credentials are a breach waiting to happen.
For third-party interactions:
- Vendors should never have admin access to the modem
- Credentials should be unique per device
- Access should be time-bound and revocable
If the modem does not support role-based access, unique credentials, or auditing, it should not be exposed directly to third parties.
Use an intermediate system that can enforce those controls instead.
Step 4: Control Access at the Application Layer
Where possible, move third-party access up the stack:
- Use application gateways
- Publish data via APIs
- Use read-only data replication
- Enforce authentication outside the modem
This shifts risk away from:
- Embedded firmware
- Weak management interfaces
- Hard-to-update devices
And into systems that are easier to patch, monitor, and audit.
Step 5: Make Offboarding a First-Class Requirement
Every third-party access design should answer one question up front:
How do we turn this off quickly?
Your process should support:
- Immediate credential revocation
- SIM deactivation if required
- Configuration rollback
- An audit trail of access history
If offboarding requires field visits or carrier involvement for routine changes, the design does not scale and will eventually fail.
Step 6: Document and Accept Residual Risk Explicitly
Even well-designed third-party access carries residual risk.
Document:
- Who has access
- What they can see
- What they can’t touch
- What happens if their credentials are compromised
Tie this back to:
- IEC 62443 zones and conduits
- Contractual security obligations
- Incident response planning
Risk that is understood and documented is manageable.
Implicit risk is not. Architectures like the one shown above succeed not because they are complex, but because they clarify where trust begins and ends.
Managing Risk at Scale: What Actually Works
Organizations that successfully manage large cellular deployments tend to do a few things consistently:
- Treat modems as OT assets, not telecom accessories
- Standardize models and hardened configurations
- Minimize exposed services and trust relationships
- Monitor SIM and traffic behavior, even if imperfect
- Plan for failure and compromise, not just prevention
At scale, variability is the enemy. Consistency is a security control.
The Hard Truth About Cellular Risk in OT
Cellular connectivity isn’t inherently insecure, but it amplifies existing weaknesses in asset management, configuration control, and lifecycle planning.
In small deployments, those weaknesses hide.
In large deployments, they compound.
If you have thousands of cellular modems in the field and can’t confidently answer:
- What firmware are they running?
- Who can access them?
- What happens if one is compromised?
Then the risk already exists, whether it’s been exploited yet or not.
Final Thought
Managing cybersecurity risk in cellular OT deployments isn’t about eliminating connectivity.
It’s about acknowledging reality and designing for it.
And if a vendor needs full modem access just to read your data, the problem isn’t the vendor, it’s the architecture.
At Enaxy, we help organizations assess and redesign cellular OT architectures with risk in mind. From modem inventory and firmware visibility to access control design and segmentation strategies, we focus on making large-scale deployments manageable, defensible, and operationally sound.
Cellular connectivity isn’t the enemy. Poor visibility and weak architecture are.
If you need help evaluating or strengthening your cellular OT deployment, contact Enaxy at info@enaxy.com.